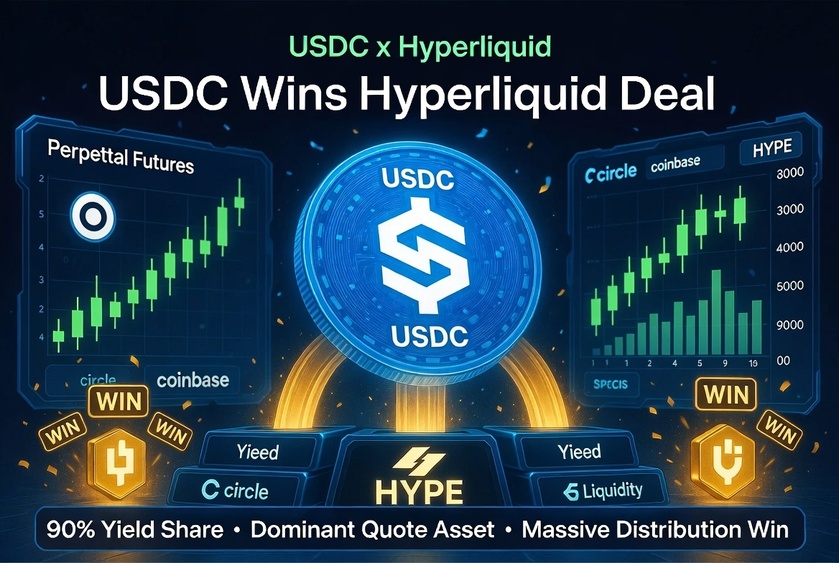
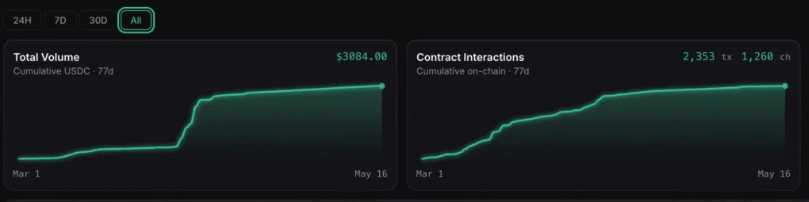
In May 2026, Native Markets sold USDH brand assets to Coinbase. USDH is being sunsetted over time (with feeless conversions/redemptions to USDC/fiat), and USDC becomes the primary/official Aligned Quote Asset on Hyperliquid. Coinbase acts as the main treasury deployer; Circle handles minting, redemptions, and cross-chain (e.g., CCTP).
How USDC Wins: 🔑 Key Advantages
Massive, sticky distribution in a high-growth venue: Hyperliquid is a leading on-chain perp DEX. USDC gains preferred status as the quote asset for most trading pairs, reducing friction vs. bridging/swapping other stables. This concentrates liquidity, improves efficiency, and funnels more capital flows through USDC.
- Deep on-chain integration: Builds on prior Native USDC + CCTP launches. Coinbase's involvement adds fiat on/off-ramps and institutional trust. USDC was already dominant (~95% of stables on the platform); this formalizes and expands it.
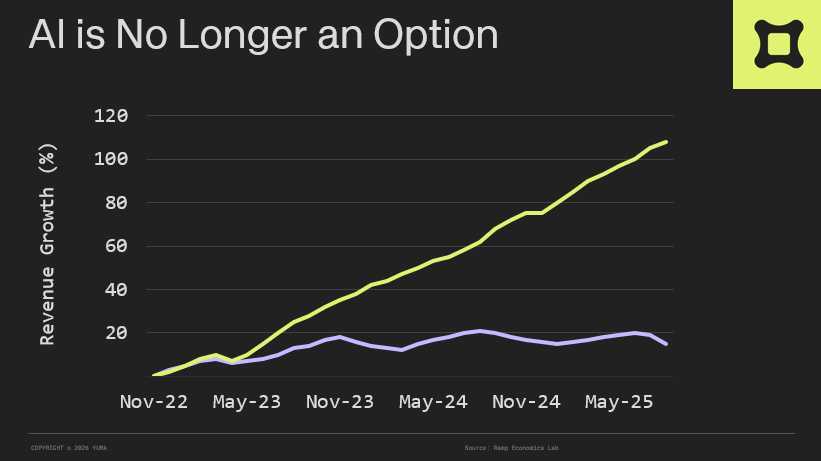
- Regulatory and brand alignment: Ties USDC to a high-profile, high-volume platform at a time when USDC has gained transaction volume momentum (surpassing USDT in some months post-regulatory clarity like GENIUS). It strengthens USDC's positioning vs. USDT (which dominates on centralized venues like Binance).
- Longer-term consolidation play: Analysts see this as part of stablecoin market consolidation around established players with liquidity and infrastructure. Fewer conversion layers = better efficiency for USDC.

The Trade-Off (and Hyperliquid's Win)Hyperliquid gets ~90% of the reserve yield (estimates: $135–160M+ annually at current balances, potentially scaling to $300–500M with growth), funneled into protocol revenue/HYPE buybacks. This is roughly double what they got from USDH and turns stablecoin balances into a resilient revenue stream (less volatile than trading fees).
For Circle/Coinbase, they give up a big share of yield (analysts estimate $60–80M hit to combined EBITDA) but retain/expand USDC's role as the backbone stable on a major platform. It's a strategic distribution win over building or competing with a new native coin.

🙏 Donations Accepted, Thank You For Your Support 🙏
If you find value in my content, consider showing your support via:
💳 Stripe:
1) or visit http://thedinarian.locals.com/donate
💳 PayPal:
2) Simply scan the QR code below 📲 or Click Here:

🔗 Crypto Donations Graciously Accepted👇
XRP: r9pid4yrQgs6XSFWhMZ8NkxW3gkydWNyQX
XLM: GDMJF2OCHN3NNNX4T4F6POPBTXK23GTNSNQWUMIVKESTHMQM7XDYAIZT
XDC: xdcc2C02203C4f91375889d7AfADB09E207Edf809A6